Food fraud, food adulteration and food crime are most highlighted terms across the food supply chain. Illegal intentional deception for economic gain using food is known as a food fraud. This risk is in all stages of the supply chain and often cross international borders. According to the EU definition food fraud usually comprises misrepresentation as well as adulteration and in some definitions also theft, tampering, diversion, tax evasion, grey market and overrun. (EU, 2014)

Fraudsters are always using food as a pawn to make easy money to maximum gains and minimize losses, which include substitution, addition, dilution, tampering or misrepresentation of food, food ingredients or food packaging: and includes false or misleading statements made about product. Different ways of fraud in the market place are:
| Dilution | Mixing a liquid ingredient of high value with a liquid of lower value |
| Substitution | Replacing an ingredient or part of the product, of high value with another ingredient, or part of the product, of lower value. |
| Concealment | Hiding the low quality of food ingredients or product. |
| Mislabelling | Placing false claims on packaging for economic gain. |
| Unapproved enhancement | Adding unknown and undeclared materials to food products to enhance the quality attributes. |
| Counterfeiting | Copying the brand name, packing concept, recipe, processing method of food products for economic gain. |
| Grey market production/ theft/diversion | Sale of excess unreported product. |
Hence it is clear that food fraud can have significant health and economic implications, but not always.
A single incident can permanently destroy a valuable brand, cause long term industry-wide losses, close off export markets and damage trust in public institutions. Recognizing this, the Global Food Safety Initiative (GFSI) required companies to conduct a food fraud vulnerability assessment and to prepare a food fraud mitigation plan.
GFSI currently recognizes the following schemes;
- BAP Seafood Processing Standard
- BRC Global Standard for Food Safety
- BRC Global Standard for storage and distribution
- BRC Global Standard for packaging and packaging materials
- Canada GAP
- China HACCP
- FSSC 22000
- Global Aquaculture Alliance Seafood
- Global G.A.P Harmonized Produce Safety Standard
- Global G.A.P Produce Safety Standard
- Global Red meat Standard
- IFS Food Standard
- IFS Logistics
- IFS PACsecure
- PrimuGFS Standard
- SQF Code
According to the GFSI guidance document it required companies to;
- Perform fraud vulnerability assessment to identify potential vulnerabilities and priorities food fraud measures.
- Have a food fraud vulnerability control plan in place the specifies the control measures the organisation has implemented to minimise the public health risk from the identified food fraud vulnerabilities and be supported by the organisation’s food safety management system.
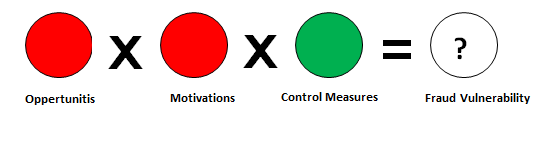
Food fraud generally occurs where the potential for and the temptation of food fraud are high and the risk of getting caught and sanctions are low. In simply the combination of opportunities (suitable target), motivations (motivated offender) and inadequate control measures (guardianship) results the fraud. That is the science based framework for understanding food fraud risk. By analysing these three aspects, you can estimate the food fraud vulnerability for any food product or ingredient.
- Opportunities – why offenders are able to commit fraud
- Motivations – why offenders would want to commit fraud
- Control measures – counteract the vulnerability resulting from opportunities and motivations.
- Opportunities-
Normally in a business every time there is a transaction, it means there is another opportunity to cheat. Opportunities can be identified as technical opportunities and opportunities in time and place. The opportunity of fraud is depend on the composition, qualities, production process, supply chain and geographic origin of food product or ingredient.
For example, liquid are more susceptible to fraud than others, complex foods with multiple ingredients generally offer greater fraud opportunity than simple-single-ingredient foods, longer supply chains result in higher food fraud risk, access of unauthorized personnel and lack of physical safeguards.
- Motivations
Motivations may due to the economic and market factors or cultural and behavioral factors. Economic motivation would be encouraged due to fulfill two main purposes: revenue maximisation or cost minimisation.
Economic and market factors –
• Special attributes that determine value
• Financial strains
• Level of competition
• Supply/demand and pricing
• Competitive strategy
• Economic health or conditions
Cultural and behavioral factors-
• Personal gains or desperation
• Ethical business culture
• Corruption level
• Victimisation
• Competitive strategy
• Blackmail
- Control Measures
Fraud control measures can counteract the vulnerability arising from opportunities and motivations. A food company’s primary fraud prevention measures are its food safety management and quality control systems, as well as food quality and safety managers and staff. Fraud controls require a similar generic approach but need to be focused on fraud issues taking into account its intentional nature. Control measures are subdivided as technical measures & managerial measures.
Technical measures refer to those aimed at detection of fraud by generating data and actual information on the prevalence of adulterated products. Maintaining monitoring systems for incoming material control that include systematic sampling plans, accurate and specific fraud detection methods, clear fraud monitoring produces and strict documentation are essential for fraud controls.
The managerial measures are more preventive in nature and aim at reducing opportunities and or motivations in the management system and the chain environment.
Specific controls include-
• Information systems (e.g. traceability, mass balance)
• Fraud monitoring and verification systems
• Whistleblowing guidelines and protections
• Ethical codes of conduct
• Legal framework and enforcement
• Social control chain network
• Contractual requirements
• Employee integrity screening
Vulnerability assessment can conducted by using simple quadratic model tool or spider web diagrams while considering the above mentioned criteria are taken into account.
The next article on steps to conduct a vulnerability assessment.
